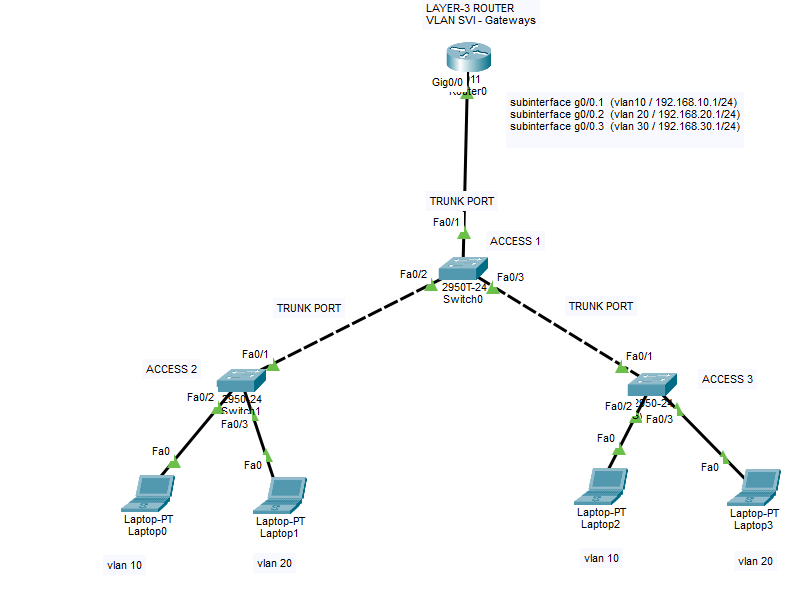
Router On A Stick Method for Layer 2 switches (ROAS Inter-vlan Legacy Communication) CISCO
In this lab, we will inspect how intervlan communication handled on Layer-3 Router with Router On a Stick model. If you have layer 2 switches for end devices, then you will need a layer 3 router or switch for intervlan communication. Layer 2 devices cannot do IP routing between VLAN gateways (SVIs) so therefore you […]
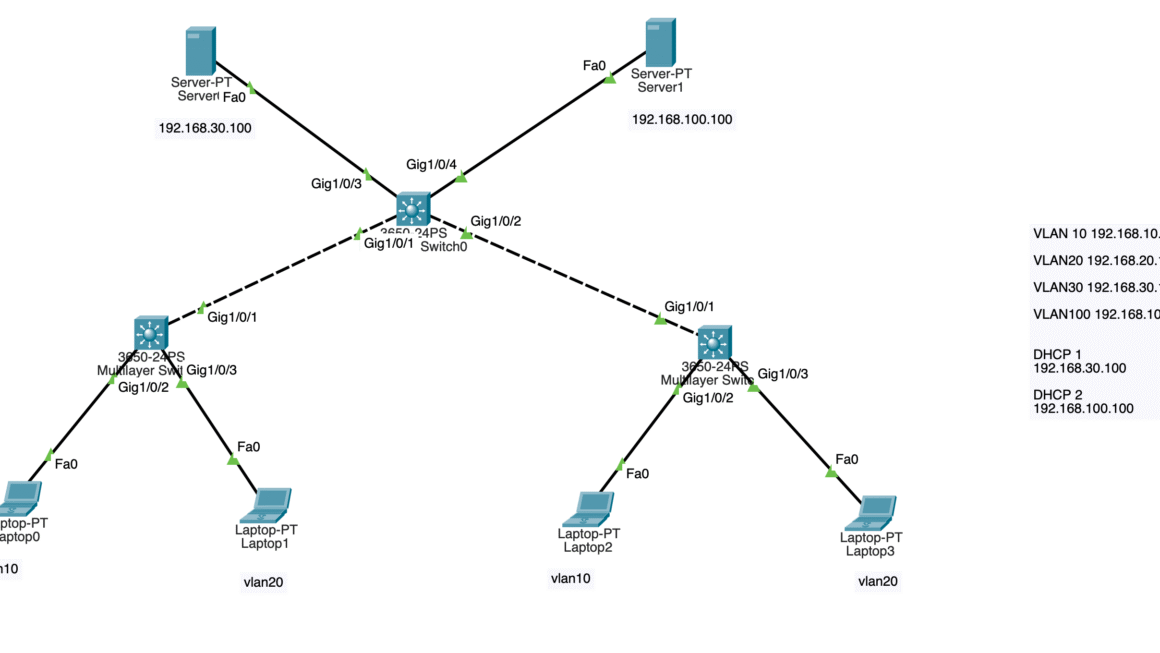
DHCP Failover configuration for VLANs
In this lab, we will simulate 2 different DHCP server on the same network for failover backup. Our primary DHCP server is 192.168.30.100 and secondary DHCP server is 192.168.100.100 . We have 4 VLANs; VLAN 10 and VLAN 20 are used for end users. VLAN 30 and VLAN 100 are used for system and network […]
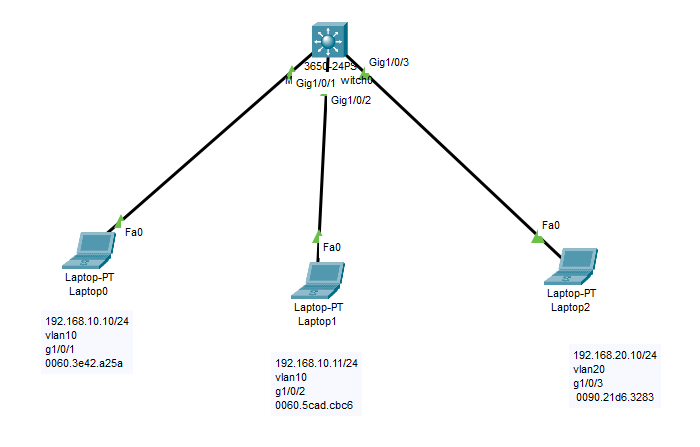
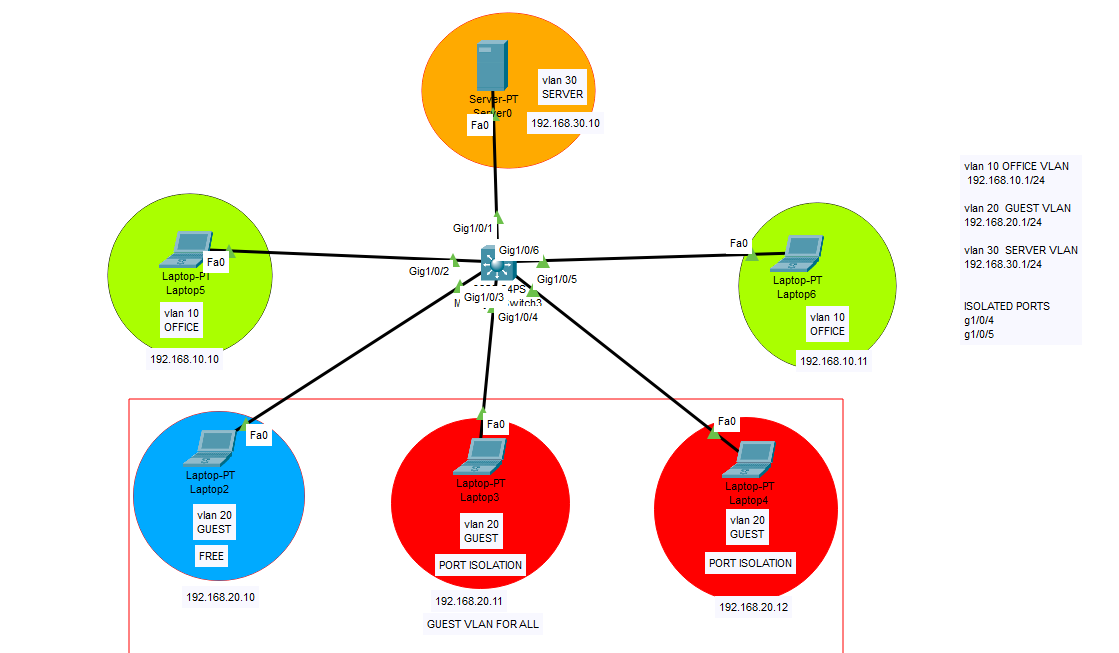
Port Isolation on VLAN subnets
This feature can be used to isolate devices in the same VLAN from each other while allowing them to access external resources (e.g., the internet, a router, or a server). It is often used in guest networks or environments where you don’t want devices in the same VLAN to communicate directly with each other. How […]
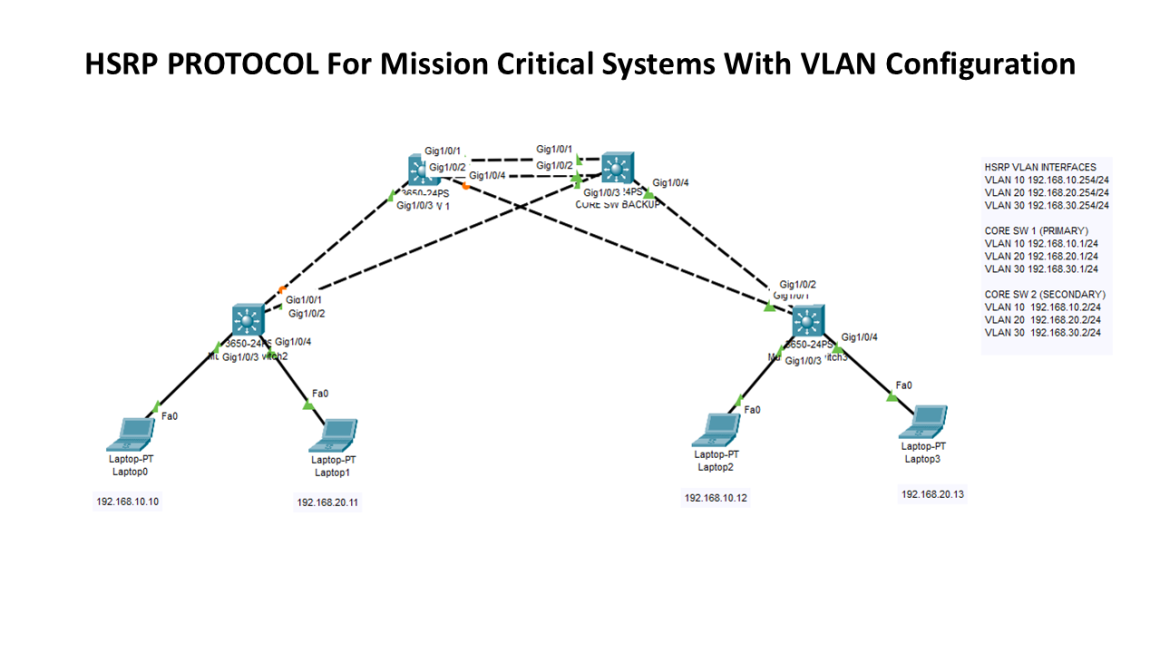
Mission Critical Systems L3 Core Switch HA
In this lab, we will use HSRP protocol to create high availability for our topology using two core switches as primary and secondary (backup) in case of a failure. By this way, we will avoid single point of failure and eliminate the system downtime. HSRP (Hot Standby Router Protocol) is a redundancy protocol developed by […]
[Hacking Series/Lab 5] –How to use CAM table overflow for attack? (MAC flooding)
Disclaimer: These methods and techniques are purely for educational and informational purposes. All attacks were carried out in an offline isolated virtual environment. The use of these techniques in normal life is illegal and the responsibility lies strictly with the reader. DO NOT USE THESE TECHNIQUES IN REAL LIFE ! A CAM table attack, also […]
[Hacking Series/Lab 4] –How to launch MAN IN THE MIDDLE Attack? (ARP poisoning)
Disclaimer: These methods and techniques are purely for educational and informational purposes. All attacks were carried out in an offline isolated virtual environment. The use of these techniques in normal life is illegal and the responsibility lies strictly with the reader. DO NOT USE THESE TECHNIQUES IN REAL LIFE ! ARP poisoning and Man-in-the-Middle (MITM) […]
[Hacking Series/Lab 1] – VLAN Hopping Attack ! This training was created for preventive defensive purposes.
Disclaimer: These methods and techniques are purely for educational and informational purposes. All attacks were carried out in an offline isolated virtual environment. The use of these techniques in normal life is illegal and the responsibility lies strictly with the reader. DO NOT USE THESE TECHNIQUES IN REAL LIFE ! In this training, I will […]
Ethernet MAC Port-security
Today we will implement port security on our Cisco switch. We will bind the MAC address of the NIC device with our related port. So if some changes happen on the physical ports, then new device will be restricted. CISCO SWITCH MAIN CONFIGURATION Switch>enable Switch#configure terminal Enter configuration commands, one per line. End with CNTL/Z. […]
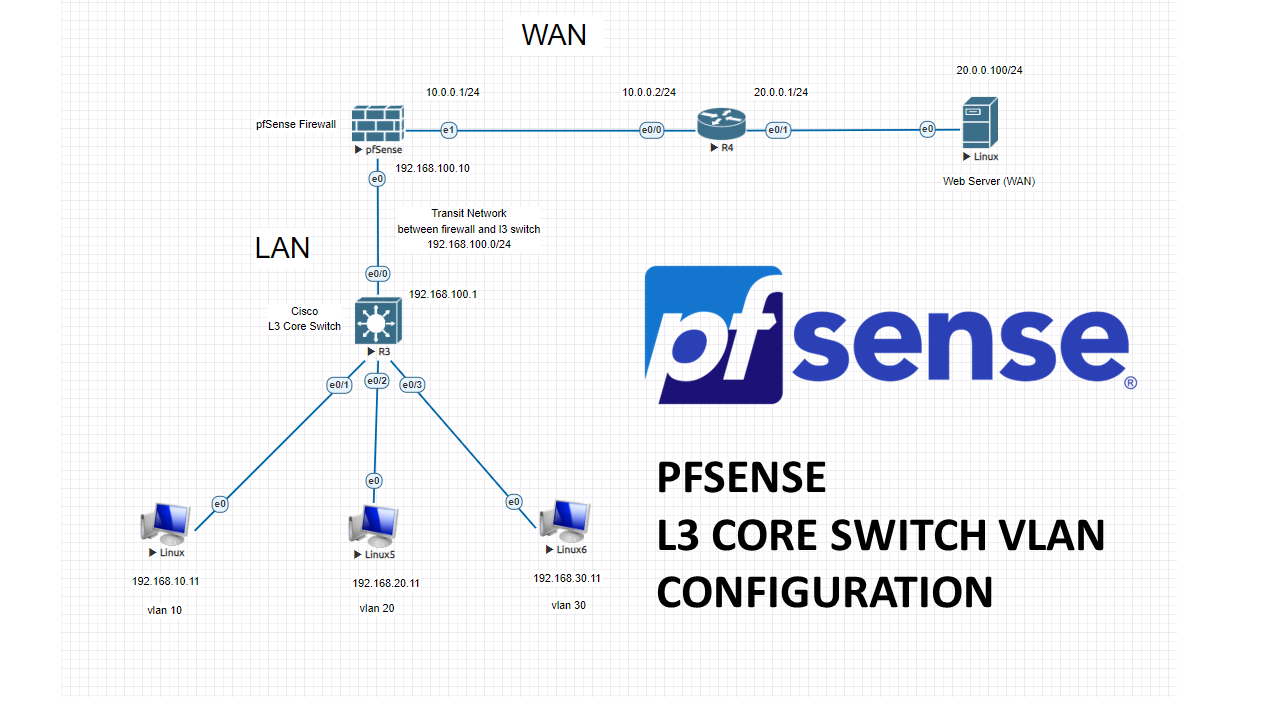
PfSense firewall + L3 Core switch configuration with VLANs
In this lab, we will create 3 vlans and connect our core switch to pfSense firewall with a transit network. Then we will configure our firewall with these vlan subnets. LAN related traffic will not hit the firewall, because SVIs (VLANgateways) will be created on L3 Core switch. All the necessary permissions between vlans will […]
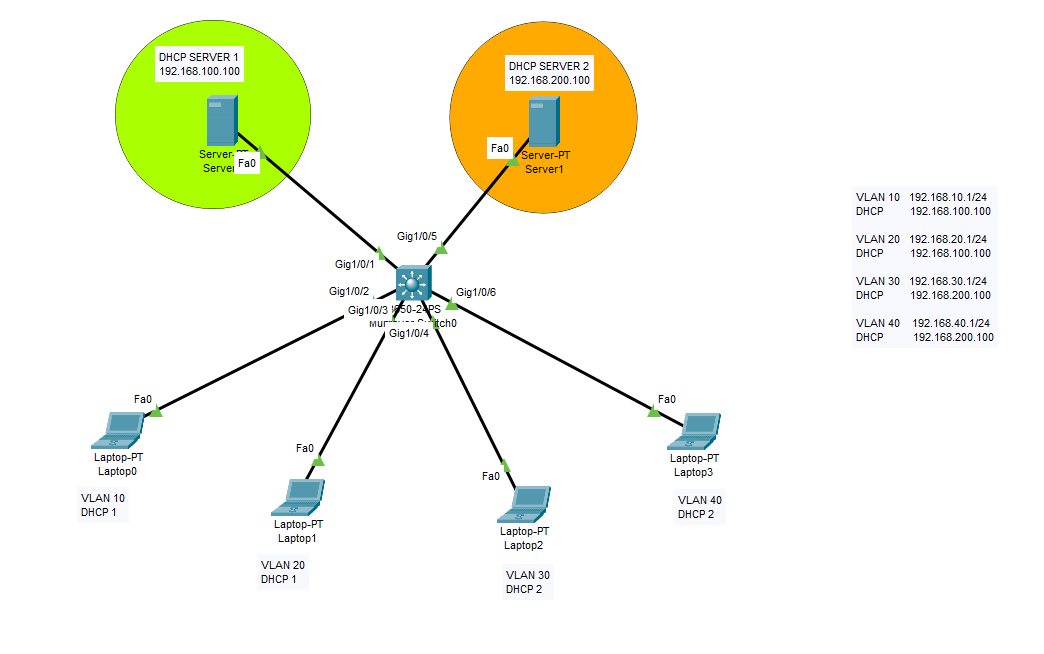
Multiple DHCP Server Configurations For VLANs
On this practice lab, we will configure two DHCP servers for 4 different VLANs. We will create the VLANs on the core switch, then we will assign the DHCP servers to VLANs with the command of “ip helper-address“. By this method, you will be able to use different DHCP servers for different purposes. Cisco Core […]
![[Hacking Series/Lab 5] –How to use CAM table overflow for attack? (MAC flooding)](https://barisyuksel.com.tr/wp-content/uploads/2024/08/macof_general1-966x653.png)
![[Hacking Series/Lab 4] –How to launch MAN IN THE MIDDLE Attack? (ARP poisoning)](https://barisyuksel.com.tr/wp-content/uploads/2024/08/mitm_diagram_topology-1035x653.png)
![[Hacking Series/Lab 1] – VLAN Hopping Attack ! This training was created for preventive defensive purposes.](https://barisyuksel.com.tr/wp-content/uploads/2024/07/vlan-hopping-diagram2.png)